Enterprise Recon 2.1
Email Locations
This section covers the following topics:
- Supported Email Locations
- Licensing
- Locally Stored Email Data
- IMAP/IMAPS Mailbox
- HCL Notes
- Microsoft Exchange (EWS)
Supported Email Locations
- Locally Stored Email Data
- IMAP/IMAPS Mailbox
- HCL Notes
- Microsoft Exchange (EWS)
Licensing
For Sitewide Licenses, all scanned email Targets consume data from the Sitewide License data allowance limit.
See Target Licenses for more information.
Locally Stored Email Data
When running a Local Storage and Local Memory scan, ER2 detects and scans offline email data stores and data files for sensitive data. ER2 does not scan data files locked by the email server.
Scanning a locally stored email data file may produce matches from ghost records or slack space that you are not able to find on the live email server itself.
- Stop the Microsoft Exchange Information Store service and back up the Microsoft Exchange Server.
- Once the backup is complete, copy the backup of the Information Store to a location that ER2 can access.
- Select that location as a Local Storage location. See Local Storage and Local Memory for more information.
IMAP/IMAPS Mailbox
To scan IMAP/IMAPs mailboxes, check that your system meets the following requirements:
| Requirements | Description |
|---|---|
| Proxy Agent |
|
| Email client | The Target Internet mailbox must have IMAP enabled. |
To Add an IMAP/IMAPS Mailbox
- From the New Scan page, Add Targets.
- In the Enter New Target Hostname field, enter the name of the IMAP/IMAPS server for the mailbox you want to scan.
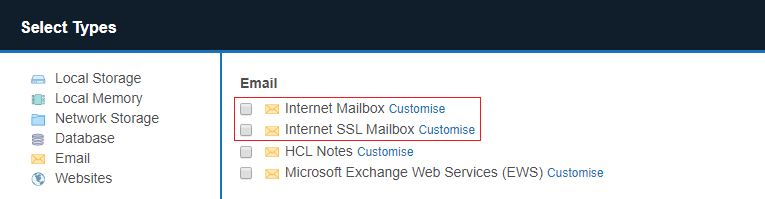
- Select the IMAP mailbox type to set up:
- IMAP: Select Email > Internet Mailbox.
- IMAPS (IMAP over SSL): Select Email > Internet SSL Mailbox.
-
In the Internet Mailbox or Internet SSL Mailbox page, fill in the following fields:
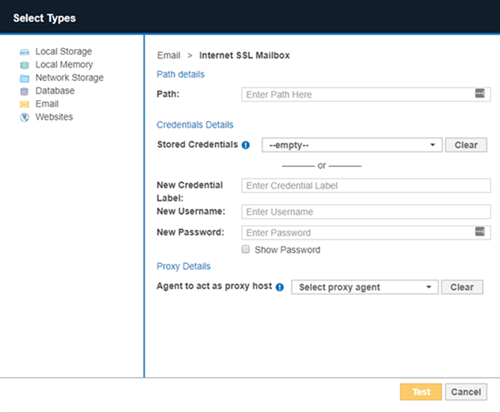
Field Description Path Enter the email address that you want to scan.
For example, <user_name@domain_name.com>.New Credential Label Enter a descriptive label for the credential set. New Username Your internet mailbox user name. Password Your internet mailbox password. Agent to act as proxy host Select a Proxy Agent host with direct Internet access. Recommended Least Privilege User ApproachData discovery or scanning of data requires read access. Remediation actions that act directly on supported file systems including Delete Permanently, Quarantine, Encryption and Masking require write access in order to change, delete and overwrite data.
To reduce the risk of data loss or privileged account abuse, the Target credentials provided for the intended Target should only be granted read-only access to the exact resources and data that require scanning. Never grant full user access privileges or unrestricted data access to any application if it is not required.
- Click Test. If ER2 can connect to the Target, the button changes to a Commit button.
- Click Commit to add the Target.
HCL Notes
To scan HCL Notes mailboxes, check that your system meets the following requirements:
| Requirements | Description |
|---|---|
| Proxy Agent |
One task at a time
Each Agent can perform only one task at a time. Attempting to perform multiple tasks simultaneously, for example, scanning and probing a Notes Target at the same time, will cause an error. To perform multiple tasks at the same time, use multiple Agents. |
| Notes client | The Agent host must have one of the following installed:
|
| Single-user installation | ER2 works best with an Agent host running a Single-user installation of the Notes client. |
| Admin user | User credentials with administrator rights to the target mailbox. |
| Others | Make sure that:
|
To Add a Notes Mailbox
- From the New Scan page, Add Targets.
- In the Enter New Target Hostname field, enter the host name of the Domino server that the Target Notes mailbox resides on.
- Click Test. If ER2 can connect to the Target, the button changes to a Commit button.
- Click Commit to add the Target.
- In the Select Types dialog box, select Email > HCL Notes.
- Fill in the fields as follows:
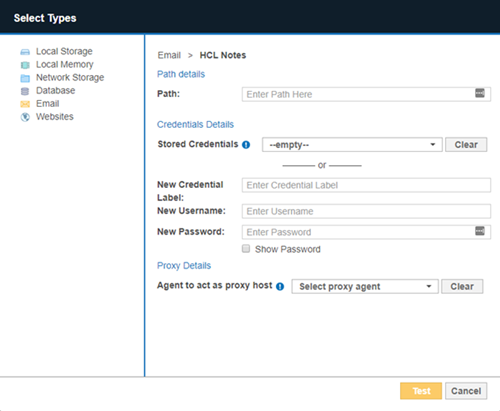
Field Description Path Enter the path to scan. Use the following syntax:
<user_name/domino_domain> is your Notes User Name.- Scans all resources available for user credentials provided.
Syntax: Leave Path blank. - Scans all resources available for the user name provided.
Syntax: <user_name/domino_domain>
Example: administrator/exampledomain - Scans a specific path available for the user credentials provided.
Syntax: <user_name/domino_domain/path>
Example: administrator/exampledomain/mail - You can specify a specific server partition to connect to.
Syntax: (partition=<server_partition_name>)
Example: (partition=serverPartitionA)Specify a server partition when:
- Connecting to a specific server partition in a Domino domain.
- The target Domino server has a server name that is different from its host name.
To connect to a specific path in serverPartitionA on a Domino server, enter:
(partition=serverPartitionA)/administrator/exampledomain/mail/administ.nsf.New Credential Label Enter a descriptive label for the credential set. New Username Your Notes User Name. New Password Your HCL Notes password. Agent to act as proxy host Select a Proxy Agent that resides on a Proxy host with the appropriate HCL Notes client installed. Recommended Least Privilege User ApproachTo reduce the risk of data loss or privileged account abuse, the Target credentials provided for the intended Target should only be granted read-only access to the exact resources and data that require scanning. Never grant full user access privileges or unrestricted data access to any application if it is not required.
- Scans all resources available for user credentials provided.
- Click Test. If ER2 can connect to the Target, the button changes to a Commit button.
- Click Commit to add the Target.
Notes User Name
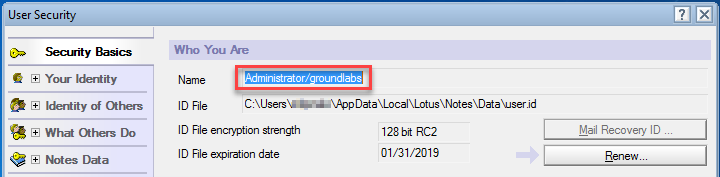
To find your Notes user name:
- Open the Notes client.
- From the menu bar, select File > Security > User Security.
- A password prompt opens. In the prompt, your Notes user name is displayed in the format <user_name/domino_domain>.
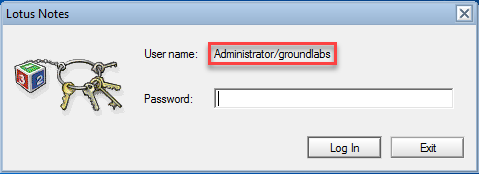
- If no password prompt opens, find your Notes user name in the User Security screen.
Microsoft Exchange (EWS)
This section covers the following topics:
- Minimum Requirements
- To Add an EWS Mailbox
- Scan Additional Mailbox Types
- Archive Mailbox and Recoverable Items
- Unsupported Mailbox Types
- Configure Impersonation
To scan a Microsoft Exchange domain instead of a single server, see Exchange Domain for more information.
- The MAPI protocol has been deprecated as of ER 2.0.17. Scan Microsoft Exchange mailboxes via Exchange Web Services (EWS).
- Scanning public folders is not supported on Exchange.
Minimum Requirements
| Requirements | Description |
|---|---|
| Proxy Agent | Agent host architecture (32-bit or 64-bit) must match the Exchange Server.
Recommended Proxy Agents:
|
| Exchange Server | Exchange Server 2007 and above. |
| Service Account | The account used to scan Microsoft Exchange mailboxes must:
|
To Add an EWS Mailbox
- From the New Scan page, Add Targets.
- In the Enter New Target Hostname field, enter the host name of your Microsoft Exchange Server.
- Click Test. If ER2 can connect to the Target, the button changes to a Commit button.
- Click Commit to add the Target.
- In the Select Types dialog box, select Email > Microsoft Exchange Web Services (EWS).
-
Fill in the fields as follows:
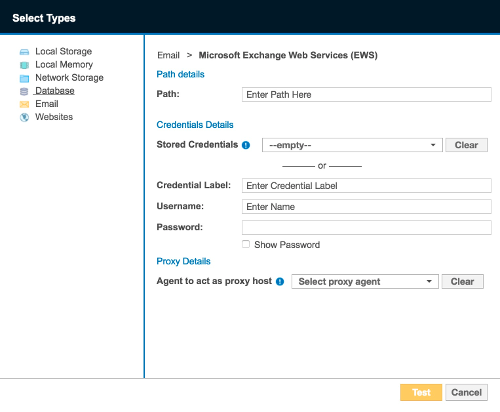
Field Description Path Enter the path to scan. Use the following syntax:
- All mailboxes
Syntax: Leave Path blank. - Specific user mailbox
Syntax: <Mailbox Display Name> - Specific folder in mailbox
Syntax: <Mailbox Display Name/folder_name>
Credential Label Enter a descriptive label for the credential set. Username <domain\username>, where username is user name of the service account created in Configure Impersonation. If your Exchange Server uses a CAS server, enter either of the following as your username:- <domain\CAS_FQDN\username>
- <domain\CAS_Array_FQDN\username>
Password Enter your service account password. Agent to act as proxy host Select a Windows Proxy Agent. - All mailboxes
- Click Test. If ER2 can connect to the Target, the button changes to a Commit button.
- Click Commit to add the Target.
Scan Additional Mailbox Types
The following additional mailbox types are supported:
- Shared mailboxes. Shared mailboxes do not have a specific owner. Instead, user accounts that need to access the shared mailbox are assigned "SendAs" or "FullAccess" permissions.
- Linked mailboxes. A linked mailbox is a mailbox that resides on one Active Directory (AD) forest, while its associated AD user account (the linked master account) resides on another AD forest.
- Mailboxes associated with disabled AD user accounts. Disabled AD user accounts may still be associated with active mailboxes that can still receive and send email. Mailboxes associated with disabled AD user accounts are not the same as disconnected mailboxes.
- Archive Mailbox and Recoverable Items
To scan the above supported mailbox types, use a service account with “FullAccess” rights to the target mailbox.
The following sections contain instructions on how to grant “FullAccess” permissions for each mailbox type:
Changes may not be immediate. Wait 15 minutes before starting a scan on the exchange server.
Once the service account is granted access to the target mailboxes, follow the instructions above to add the shared mailbox as a Target.
You cannot use a linked master account (the owner of a linked mailbox) to scan Exchange Targets in ER2. To successfully scan an Exchange Target, use a service account that resides on the same AD forest as the Exchange Target.
Shared Mailboxes
To grant a service account "FullAccess" rights to shared mailboxes, run the following commands in the Exchange Management Shell:
-
To grant a user full access to a specific shared mailbox:
Add-MailboxPermission -Identity <SHARED_MAILBOX> -User <SERVICE_ACCOUNT> -AccessRights FullAccess -Automapping $falsewhere <SHARED_MAILBOX> is the name of the shared mailbox, and <SERVICE_ACCOUNT> is the name of the account used to scan the mailbox. -
To grant a user full access to all existing shared mailboxes on the Exchange server:
Get-Recipient -Resultsize unlimited | where {$_.RecipientTypeDetails -eq "SharedMailbox"} | Add-MailboxPermission -User <SERVICE_ACCOUNT> -AccessRights FullAccess -Automapping $falsewhere <SERVICE_ACCOUNT> is the name of the account used to scan the mailboxes.
Linked Mailboxes
To grant a service account "FullAccess" rights to linked mailboxes, run the following commands in the Exchange Management Shell:
-
To grant a user full access to a specific shared mailbox:
Add-MailboxPermission -Identity <LINKED_MAILBOX> -User <SERVICE_ACCOUNT> -AccessRights FullAccess -Automapping $falsewhere <LINKED_MAILBOX> is the name of the shared mailbox, and <SERVICE_ACCOUNT> is the name of the account used to scan the mailbox. -
To grant a user full access to all existing shared mailboxes on the Exchange server:
Get-Recipient -Resultsize unlimited | where {$_.RecipientTypeDetails -eq "LinkedMailbox"} | Add-MailboxPermission -User <SERVICE_ACCOUNT> -AccessRights FullAccess -Automapping $falsewhere <SERVICE_ACCOUNT> is the name of the account used to scan the mailboxes.
Mailboxes associated with disabled AD user accounts
To grant a service account "FullAccess" rights to mailboxes associated with disabled AD user accounts, run the following commands in the Exchange Management Shell:
-
To grant a user full access to a specific mailbox:
Add-MailboxPermission -Identity <USER_DISABLED_MAILBOX> -User <SERVICE_ACCOUNT> -AccessRights FullAccess -Automapping $falsewhere <USER_DISABLED_MAILBOX> is the name of the mailbox associated with a disabled AD user account, and <SERVICE_ACCOUNT> is the name of the account used to scan the mailbox.
Archive Mailbox and Recoverable Items
Requirements: Exchange Server 2010 SP1 and newer.
When enabled for a user mailbox, the Archive mailbox and the Recoverable Items folder can be added to a scan:
- Archive or In-Place Archive mailboxes.
An archive mailbox is an additional mailbox that is enabled for a user's primary mailbox, and acts as long-term storage for each user account.
Archive mailboxes are listed as (ARCHIVE) on the Select Locations page when browsing an Exchange mailbox. - Recoverable Items folder or dumpster.
When enabled, the Recoverable Items folder or the dumpster in Exchange retains deleted user data according to retention policies.
Recoverable Items folders are listed as (RECOVERABLE) on the Select Locations page when browsing an Exchange mailbox.
By default, adding a user mailbox to a scan also adds the user's Archive mailbox and Recoverable Items folder to the scan.
To add only the Archive mailbox or Recoverable Items folder to the scan:
- Configure impersonation for the associated user mailbox. See Configure Impersonation for more information.
- Add the Exchange Target to the scan.
- In the Select Locations page, expand the added Exchange Target and browse to the Target mailbox.
- Expand the target mailbox, and select (ARCHIVE) or (RECOVERABLE).
Unsupported Mailbox Types
ER2 currently does not support the following mailbox types:
- Disconnected mailboxes. Disconnected mailboxes are mailboxes that have been:
- Disabled. Disabled mailboxes are rendered inactive and retained until the retention period expires, while leaving associated user accounts untouched. Disabled mailboxes can only be accessed by reconnecting the owner user account to the mailbox.
- Removed. Removing a mailbox deletes the associated AD user account, renders the mailbox inactive and retains it until its retention period expires. Disabled mailboxes can only be accessed by connecting it to another user account.
- Moved to a different mailbox database. Moving a mailbox from one mailbox database to another leaves the associated user account untouched, but sets the state of the mailbox to "SoftDeleted". "SoftDeleted" mailboxes are left in place in its original mailbox database as a backup, in case the destination mailbox is corrupted during the move. To access a "SoftDeleted" mailbox, connect it to a different user account or restore its contents to a different mailbox.
- Resource mailboxes. Resource mailboxes are mailboxes that have been assigned to meeting locations (room mailboxes) and other shared physical resources in the company (equipment mailboxes). These mailboxes are used for scheduling purposes.
- Remote mailboxes. Mailboxes that are set up on a hosted Exchange instance, or on Microsoft 365, and connected to a mail user on an on-premises Exchange instance.
- System mailboxes.
- Legacy mailboxes.
The following are not mailboxes, and are not supported as scan locations:
- All distribution groups.
- Mail users or mail contacts.
- Public folders.
Configure Impersonation
To scan a Microsoft Exchange mailbox, you can:
- Use an existing service account, and assign it the ApplicationImpersonation management role, or
- (Recommended) Create a new service account for use with ER2 and assign it the ApplicationImpersonation management role.
Service accounts are user accounts set up to perform administrative tasks only. Because of the broad permissions granted to service accounts, we recommend that you closely monitor and limit access to these accounts.
Assigning a service account the ApplicationImpersonation role allows the account to behave as if it were the owner of any account that it is allowed to impersonate. ER2 scans those mailboxes using permissions assigned to that service account.
To assign a service account the ApplicationImpersonation role for all mailboxes:
-
On the Exchange Server, open the Exchange Management Shell and run as administrator:
# <impersonationAssignmentName>: Name of your choice to describe the role assigned to the service account. # <serviceAccount>: Name of the Exchange administrator account used to scan EWS. New-ManagementRoleAssignment –Name:<impersonationAssignmentName> –Role:ApplicationImpersonation –User:<serviceAccount>
(Advanced) To assign the service account the ApplicationImpersonation role for a limited number of mailboxes, apply a management scope when making the assignment.
To assign a service account the ApplicationImpersonation role with an applied management scope:
- On the Exchange Server, open the Exchange Management Shell as administrator.
-
Create a management scope to define the group of mailboxes the service account can impersonate:
New-ManagementScope -Name <scopeName> -RecipientRestrictionFilter <filter>For more information on how to define management scopes, see Microsoft: New-ManagementScope. -
Apply the ApplicationImpersonation role with the defined management scope:
New-ManagementRoleAssignment –Name:<impersonationAssignmentName> –Role:ApplicationImpersonation –User:<serviceAccount> -CustomRecipientWriteScope:<scopeName>